Over the last few months, autonomous cyberattacks have decisively crossed the threshold from theoretical to operational. In perhaps the most publicly documented case, Anthropic* published a detailed account last November of disrupting what they termed a “90% autonomous” cyber espionage campaign. AI agents conducted reconnaissance across multiple target environments, progressed through privilege escalation without human guidance, and coordinated data exfiltration while adapting to defensive measures.
This campaign represents something security researchers have been tracking closely over the past 24 months: The performance gap between AI and human operators in offensive security tasks has not just narrowed; it has reversed. Where AI systems once required human oversight at each decision point, they now operate with increasing autonomy across the full attack chain. The same architecture behind viral tools like OpenClaw—persistent, autonomous, tireless—is what makes AI-powered offensives difficult to defend against. Importantly, the implications extend far beyond just faster attacks. When the primary constraint on security validation shifts from human expertise to compute, the model of how organizations test and validate their security posture changes with it. This is precisely the world we described in our Agents for Security article last fall: one where the speed and autonomy of the threat renders human-scale detection obsolete.
The question heading into RSA 2026 is no longer whether AI can autonomously exploit vulnerabilities; it’s how organizations keep up. This, in large part, motivated Menlo’s recent investment in Armadin*: When attacks are autonomous and continuous, human-led engagements fail to keep pace. Armadin deploys a swarm of specialized AI agents to continuously probe an organization’s full attack surface and surface-exploitable kill chains at machine speed, 24/7.
When AI Started Outperforming Human Pentesters
To understand how far things have come, it helps to start with what AI systems were capable of in early 2023. At that point, AI’s role in offensive security was primarily assistive: Language models generated phishing content, helped analysts prioritize vulnerability scanner output, and augmented manual reconnaissance. The work remained fundamentally human-driven. Performance benchmarks reflected these limitations—AI-generated phishing underperformed elite human red teams by 18%—and exploitation required human oversight at each decision point.
By March 2025, the landscape had shifted measurably: AI-generated phishing outperformed humans by 24%, a 42-percentage-point swing in two years. Anthropic’s Cybench progression shows similar acceleration: Claude Sonnet 4.5 doubled its success rate from 38% to 76.5% in six months when given 10 attempts per challenge. (Defensive vendors like Abnormal AI* have made meaningful progress countering AI-generated phishing specifically, though the arms race across the broader attack surface continues to accelerate.)
Three technical developments were key to this acceleration:
- Extended reasoning allows models to maintain context across the full attack chain, where reconnaissance findings inform exploitation attempts, which shape post-exploitation actions.
- Tool integration has evolved from generating commands for human execution to directly manipulating security frameworks.
- Multi-modal capabilities compound these advances: Vision models can analyze network diagrams, interpret application UI flows, and extract patterns from infrastructure screenshots, automating reconnaissance tasks that previously required human analysts.
And, importantly, the improvements compound. Extended reasoning makes tool use more effective. Tool use generates richer data for multi-modal analysis. Multi-modal analysis provides better context for reasoning. As a result, AI capabilities in certain offensive security domains are beginning to exceed human baselines, not just approach them.
Why Offense Advances Faster
Recent research from Anthropic and Google DeepMind calls out structural reasons why offensive AI capabilities advance faster than defensive applications. Offensive operations produce immediate, verifiable feedback—whether a system is breached or not—which makes them highly amenable to reinforcement learning. Defensive success, on the other hand, requires comprehensive coverage with no equivalent signal. Blocking one attack vector and leaving nine others intact registers as neither a success or failure, which makes it substantially harder to train defensive agents on the same RL techniques. Moreover, attackers leverage unconstrained models and custom training data, while defenders work within commercial models with safety restrictions. Defenders must continuously analyze entire attack surfaces, while attackers selectively target high-value systems. These factors compound to create economic and technical asymmetry at scale.
Multi-modal capabilities amplify this gap by automating reconnaissance tasks that previously required human analysts. The result is a feedback loop where offensive capabilities advance faster, successful attacks generate training data, and the gap widens. The evidence is measurable: Amazon reported 100 million threats daily in early 2024, then 750 million by year-end, a 7.5x increase.
This structural asymmetry, while challenging for defenders, creates substantial opportunity for companies building offensive AI platforms. The growing gap between attacker capabilities and traditional defensive approaches means enterprises face increasing pressure to adopt AI-powered security validation.
Pentesting Is Just the Tip of the Iceberg
Vulnerability and threat exposure management companies (like Zafran*) aim to answer the same question pentesting does—what’s exploitable in my environment—but from the inside out, using scanners and asset inventories. Defenders and attackers simply see the same environment differently. Pentesting has always been valuable precisely because it replicates the outside-in attacker perspective that defensive tooling approaches from a different angle. But at quarterly cadences and 20-25% surface coverage, the signal was always incomplete. AI changes the economics of that outside-in view, and, in doing so, starts to address the asymmetry that has long favored attackers: For the first time, defenders can probe their environment with the same speed, breadth, and persistence as the threats they’re defending against.
What this means in practice is that “offensive AI” goes well beyond faster pentesting. Traditional security validation operates on a simple constraint: Human expertise is scarce and expensive, so organizations test periodically, cover a fraction of their attack surface, and accept the gaps between assessments. AI removes that constraint entirely, unlocking use cases that manual engagements could never support—continuous red teaming that keeps pace with development velocity, phishing simulations that adapt in real time to target behavior, attack path simulation that maps lateral movement across entire enterprise environments, and autonomous agentic workflows that chain reconnaissance, exploitation, and post-exploitation without human handoffs.
The Emerging Landscape of Offensive AI
The capability improvements have catalyzed a wave of new companies building AI-powered offensive security platforms. The market is bifurcating along lines that mirror the broader “AI for security” versus “security for AI” divide: Some companies focus on traditional enterprise infrastructure, while others target AI systems themselves.
The bifurcation reflects distinct technical problems. Enterprise infrastructure security addresses vulnerability classes with decades of research and established taxonomies: SQL injection, cross-site scripting, privilege escalation. The challenge is automation and scale. AI system security addresses vulnerabilities that remain poorly understood: prompt injections that succeed technically but don’t violate model policies, data leakage through subtle model behaviors, adversarial inputs that manipulate reasoning processes. The challenge is understanding what “secure” means for probabilistic systems where outputs aren’t deterministic.
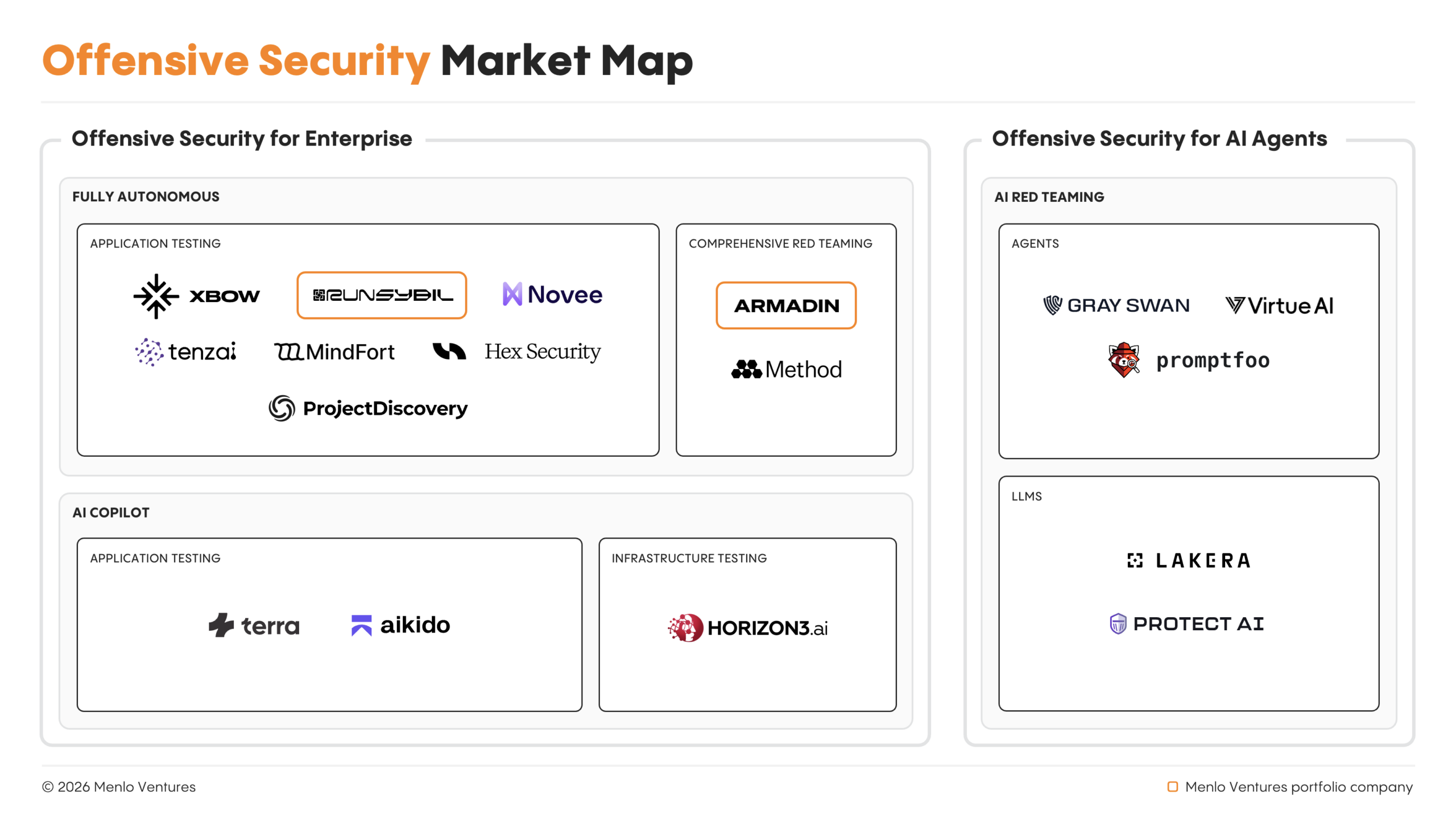
Offensive AI for Enterprise Apps and Infra
For enterprise infrastructure testing, two approaches have emerged. Compliance-focused companies sell $50,000–$150,000 solutions to mid-market buyers who need faster pentests for certifications, capturing share of the existing $6 billion services market while facing commoditization risk. Continuous security platforms (like Armadin) target large enterprises with $250,000–$1 million+ contracts for autonomous, 24/7 testing across full attack surfaces, enabling organizations to validate security posture continuously rather than periodically. In doing so, AI-native platforms unlock budget expansion by solving a different problem—not just faster compliance testing, but security validation that matches modern development velocity.
Offensive AI for AI Models and Agents
AI model testing addresses a different problem than traditional pentesting. Testing a web application involves identifying whether inputs trigger known vulnerability patterns—SQL injection, authorization bypasses. Testing an AI model involves understanding whether a probabilistic system can be manipulated through prompts or interaction patterns to behave in unintended ways, with no clear boundary between “working as designed” and “exploited.”
The competitive dynamic for AI model testing is complicated by frontier labs themselves. OpenAI, Anthropic, and others maintain internal red teams with direct access to state-of-the-art models, proprietary training data, and deep model integration. While these frontier labs may partner with external providers, valuing independent perspectives and crowdsourced scale, how this relationship endures as internal capabilities mature remains to be decided. For external platforms to succeed long term, they need capabilities that labs cannot easily replicate: network effects from aggregating data across multiple labs or workflow integrations that become embedded in security processes.
An Important Consideration: Data
The performance of offensive AI systems depends largely on their training data, but offensive security lacks natural datasets at scale. Successful penetration tests are proprietary, conducted under NDA, and rarely published. As a result, we’ve seen a few approaches emerge to solve this constraint:
- Public data sources. CVE databases, disclosed vulnerabilities, published exploit code, security research papers, etc. form the baseline. Every company building in this space likely leverages these datasets, making them table stakes.
- Bringing pentesters in-house. Companies can employ elite penetration testers to generate labeled training data: conducting actual attacks, documenting full exploitation chains, and labeling successful versus unsuccessful approaches including reasoning behind technique selection. As a result, human-labeled data reflects actual vulnerability patterns and captures the intuition that guides security experts. The main consideration, however, is cost: Elite pentesters command six-figure salaries, and the approach struggles to scale without proportional cost increases.
- Synthetic data. Multi-agent architectures deploy specialized sub-agents handling different pentesting phases—discovery, validation, reporting—that learn from testing each other through reinforcement learning. While this solves the scaling problem, the risk you undertake here is in quality and validity.
- Crowdsourced data. For example, Gray Swan’s Arena platform operates with 15,000+ red teamers competing to break AI models through prize incentives rather than salaries. This has generated millions of adversarial attempts across multiple frontier labs (OpenAI, Anthropic, Meta) and provides a strong data advantage so long as the applications of your AI pentests are the same as what you’ve gathered data for.
Whether data advantages persist as foundation models improve remains to be seen. If data advantages compound through network effects, these early movers will have built insurmountable positions. If foundation model improvements compress the gap, the companies that have already built distribution and integration advantages alongside their data will be best positioned to capitalize.
The Path Forward
The market opportunity extends well beyond the $6 billion in traditional pentesting services. When you include bug bounties, red team programs, and the broader offensive security consulting market, the addressable opportunity is substantially larger. More importantly, lowering the barrier to continuous testing will only expand total spend: Enterprises currently test only 20-25% of applications due to cost and availability constraints. AI-native platforms that enable 100% coverage unlock latent demand that was previously suppressed by economics.
Still, the market is in its early days. Success will require developing advantages that compound over time—whether through proprietary data aggregation, deep workflow integration, or building trust with enterprises willing to grant autonomous systems access to production infrastructure. The companies that execute on these advantages will define how the next generation of enterprises validates security in an AI-first world.
If you’re building security systems that use agents to match the pace of AI-driven attacks, we’d love to talk.
*Menlo Ventures portfolio company
Venky is a partner at Menlo Ventures focused on investments in both the consumer and enterprise sectors. He currently serves on the boards of Abnormal AI, Appdome, Aurascape, BitSight, ConverzAI, MealPal, Obsidian, Sonrai Security, and Unravel Data. He previously led investments in and served on the boards of Aisera (acquired…
Rama is a partner at Menlo Ventures, focused on investments in cybersecurity, AI, and cloud infrastructure. He is passionate about partnering with founders to build the next generation of cybersecurity, infrastructure, and observability companies for the new AI stack. Rama joined Menlo after 15 years at Norwest Venture Partners, where…
As an investor at Menlo Ventures, Sam focuses on SaaS, AI/ML, and cloud infrastructure opportunities. She is passionate about supporting strong founders with a vision to transform an industry. Sam joined Menlo from the Boston Consulting Group, where she was a core member of the firm’s Principal Investors and Private…
Sabrina is an investor at Menlo Ventures, where she focuses on inflection-stage companies in enterprise SaaS, AI/ML, and cloud infrastructure. She’s excited about partnering with founders who challenge the status quo and supporting them in transforming bold visions into enduring businesses. Her passion for startups began at Fastcase (now vLex),…